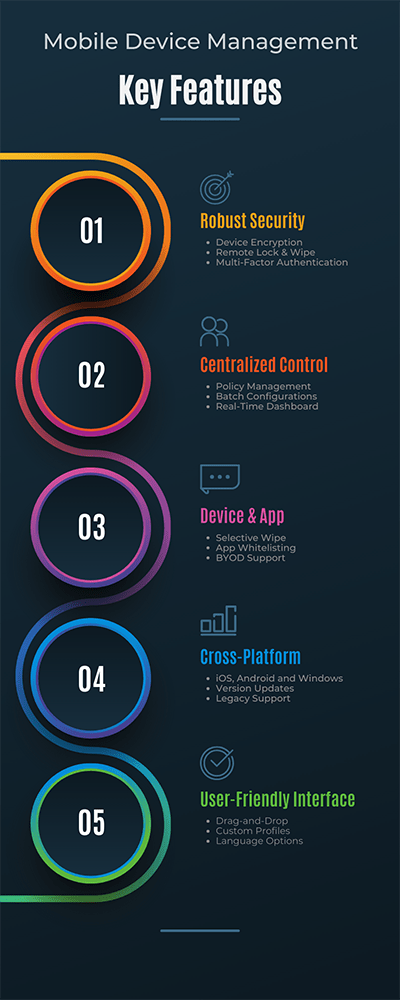
Key Features of Mobile Device Management Solutions
Managing mobile devices across your organization shouldn't be a headache. Discover how our suite of MDM solutions can make your life easier and more secure.
Robust Security Measures
- Device Encryption: Protect sensitive data with industry-standard encryption.
- Remote Lock & Wipe: Remotely lock or erase data on lost or stolen devices.
- Multi-Factor Authentication: Add an extra layer of security to ensure only authorized users can access the system.
Centralized Control
- Dashboard: Real-time insights and analytics on all connected devices.
- Policy Management: Easily set and enforce security policies across all devices.
- Batch Configuration: Configure multiple devices simultaneously with the click of a button.
Device & App Management
- Selective Wipe: Remove only company data while leaving personal data untouched.
- App Whitelisting: Control which apps can be installed on the devices.
- BYOD Support: Seamless support for employee-owned devices.
Cross-Platform Compatibility
- iOS, Android, and Windows: Consistent experience across all major operating systems.
- Version Updates: Automatically receive and implement software updates.
- Legacy Support: Management solutions for older devices and systems.
User-Friendly Interface
- Drag-and-Drop: Simple, intuitive controls for effortless management.
- Custom Profiles: Tailor device settings to individual needs and roles within your organization.
- Language Options: Available in multiple languages for global operability.
24/7 Customer Support
- Real-Time Assistance: Our experts are just a call or click away.
- Knowledge Base: A comprehensive library of guides and tutorials.
- On-Site Support: Available for complex setups and emergency situations.
Benefits of Implementing MDM in Your Organization
In today's digital age, the use of mobile devices in the workplace has gone from a luxury to a necessity. Smartphones, tablets, and even wearables are being increasingly used to perform tasks previously confined to desktop computers. However, this widespread use of mobile technology comes with its own set of challenges, including security threats, data management issues, and operational inefficiencies. This is where Mobile Device Management comes in. Here are the key benefits your organization stands to gain by implementing an MDM solution:
Enhanced Security
The single biggest benefit of MDM is the robust security features it offers. From protecting sensitive corporate data with encryption to the ability to remotely lock and wipe devices, MDM ensures that your data is safe even in the event of theft or loss. Multi-factor authentication adds an additional layer of security, minimizing the risk of unauthorized access.
Streamlined Operations
The centralized control dashboard is a game-changer when it comes to streamlining operations. IT administrators can manage devices, monitor performance, and enforce policies from a single interface. This not only simplifies the management process but also saves countless hours, thereby increasing operational efficiency.
Policy Uniformity
Setting and enforcing policies across various devices can be a challenging task. With MDM, you can easily configure policies for groups of devices, ensuring that all gadgets meet the minimum security and performance benchmarks. This ensures consistency and uniformity in the way mobile devices are used within the organization.
Cost-Effectiveness
While the initial setup may require some investment, the long-term benefits are more than worth it. The efficiencies gained through streamlined operations, automated processes, and reduced manual interventions translate to significant cost savings. Plus, the savings from preventing a single data breach alone could offset the cost of implementing an MDM system.
Device and App Management
MDM solutions offer flexibility in managing both company-owned and BYOD (Bring Your Own Device) policies. With features like selective wiping and app whitelisting, companies can exercise a great deal of control over how company resources are utilized without infringing on personal use. Employees can use their preferred devices and apps for work without compromising security, which can also improve job satisfaction and productivity.
Cross-Platform Compatibility
In the modern workplace, it's common to find a mix of Android, iOS, and Windows devices. A quality MDM solution offers cross-platform support, allowing organizations to manage devices running on different operating systems seamlessly. This is particularly beneficial for companies with a diverse mobile ecosystem.
Ease of Scaling
As your company grows, so will your need for more devices and increasingly complex mobile infrastructure. An MDM solution can effortlessly scale to meet these demands. You can add new devices, configure settings, and roll out updates, all without having to start from scratch each time.
Legal and Regulatory Compliance
Staying compliant with industry regulations and laws can be a huge undertaking, particularly when it involves mobile devices that store or access sensitive data. MDM solutions help maintain compliance through features like audit trails, encryption, and policy enforcement, making it easier for organizations to meet legal obligations.
Employee Mobility
With the shift towards remote working and flexible work schedules, employee mobility has become a significant aspect of modern work culture. MDM solutions empower employees to work from anywhere, offering them access to critical business data and applications securely, thereby improving overall productivity and job satisfaction.
Business Continuity
In case of device failures, or even natural disasters, MDM solutions enable rapid data recovery and device re-provisioning. This ensures that your business operations are not interrupted, thereby contributing to improved business continuity plans.
Rich Analytics and Reporting
Advanced MDM solutions offer analytics and reporting tools that provide valuable insights into device usage, app performance, and more. These insights can be used to make informed decisions and further fine-tune your mobile device policies.
Competitive Advantage
In a market where even the smallest advantage counts, having a streamlined, secure, and efficient mobile device environment can set you apart from competitors. It shows your commitment to security and efficiency, making you more appealing to clients and potential business partners.
Mobile Device Management FAQ
Answer: Mobile Device Management is a type of security software used by IT departments to monitor, manage, and secure employees' mobile devices, including smartphones, tablets, and laptops. MDM allows for centralized administration, enforcing policies, and implementing security measures across a range of devices, both company-owned and BYOD (Bring Your Own Device).
Answer: MDM is crucial for any organization that uses mobile devices for business purposes. It helps in streamlining operations, enhancing security measures, and ensuring that all devices meet the organization's policy requirements. With the increasing number of security threats targeting mobile devices, having an MDM solution is vital for protecting sensitive data and maintaining compliance with regulatory standards.
Answer: Most modern MDM solutions offer cross-platform support for a variety of devices and operating systems including iOS, Android, and Windows. This allows you to manage a diverse range of devices within your organization seamlessly.
Answer: MDM is beneficial for organizations of all sizes. While large enterprises may have more complex needs and a greater number of devices to manage, small businesses also stand to benefit from the enhanced security and operational efficiencies that MDM provides. Many MDM solutions offer scalable plans to fit the needs and budgets of smaller organizations.
Answer: Yes, most MDM solutions offer BYOD management features that allow you to secure and manage employee-owned devices that are used for business purposes. Features like selective wipe enable you to erase only the business data from the device, leaving personal data untouched, making it easier to manage a BYOD environment securely.
Answer: The complexity of implementing an MDM solution varies depending on the size of your organization and the specific needs you have. However, most modern MDM solutions are designed to be user-friendly and come with comprehensive guides and customer support. Many also offer the services of a dedicated account manager to assist with setup and ongoing management.
